Sentinel
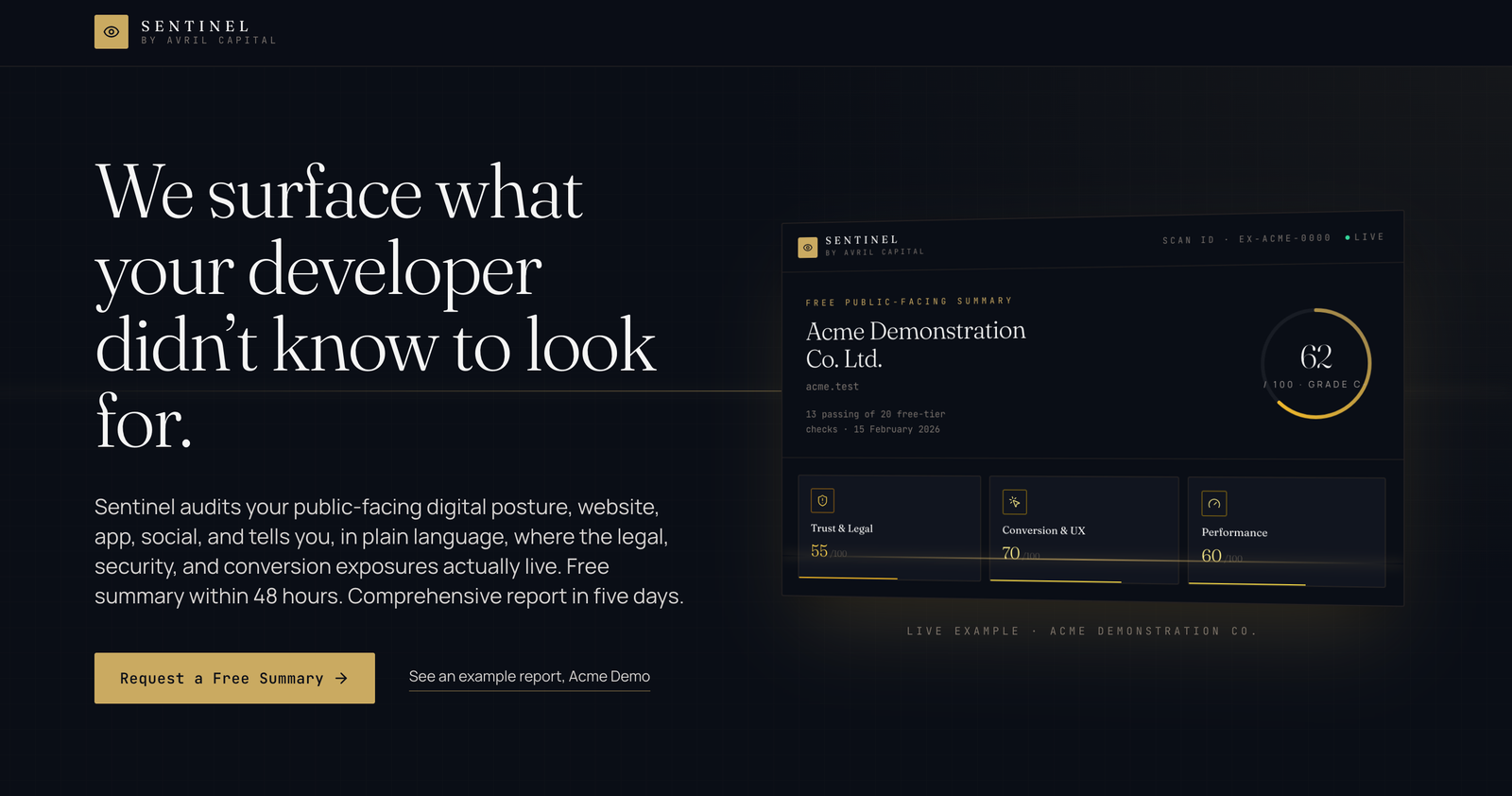
We surface what your developer didn't know to look for.
Sentinel is Avril Capital's proprietary audit platform. It tells you, in plain language, where the legal, security, and conversion exposures actually live across your website, app, and social presence. Free public-facing summary in 48 hours. Boardroom-ready report with CVSS-scored findings and a prioritized remediation playbook in five business days.
The Sentinel framework evaluates your public-facing surface across seven dimensions: Trust and Legal, Conversion and UX, Performance and Mobile, Search and Discoverability, AI Implementation, Security and Hardening, and an Authorized Penetration Test. The optional Implementation tier remediates Critical and High findings before the report is handed over, with five guaranteed deliverables: email-authentication publication (SPF, DKIM, DMARC), HTTP security-headers deployment, image-format optimization, form-consent flow drafting, and Privacy Policy template drafting.
Surface // Public-Facing Posture
Free summary, then comprehensive CVSS-scored report. Optional Implementation tier remediates critical and high findings.
Perimeter // Org-Wide Deep Posture
Full attack-surface and configuration audit, scoped to org size, with a 90-day rescan retainer.
Sentinel Executive // C-Suite Digital Risk
The personal layer. Per-executive digital footprint, leaked-credential monitoring, family attack-surface mapping, doxxing and impersonation risk, deepfake and synthetic-media surveillance, and quarterly briefings written for the executive, not the IT department.